In recent weeks, several signals have coincided which, seen separately, look like different stories: more cybersecurity incidents, new phishing campaigns, European movement around NIS2 and Cybersecurity Act 2, AI Act obligations getting closer and an AEPD 2026 action plan strongly focused on technology and AI.
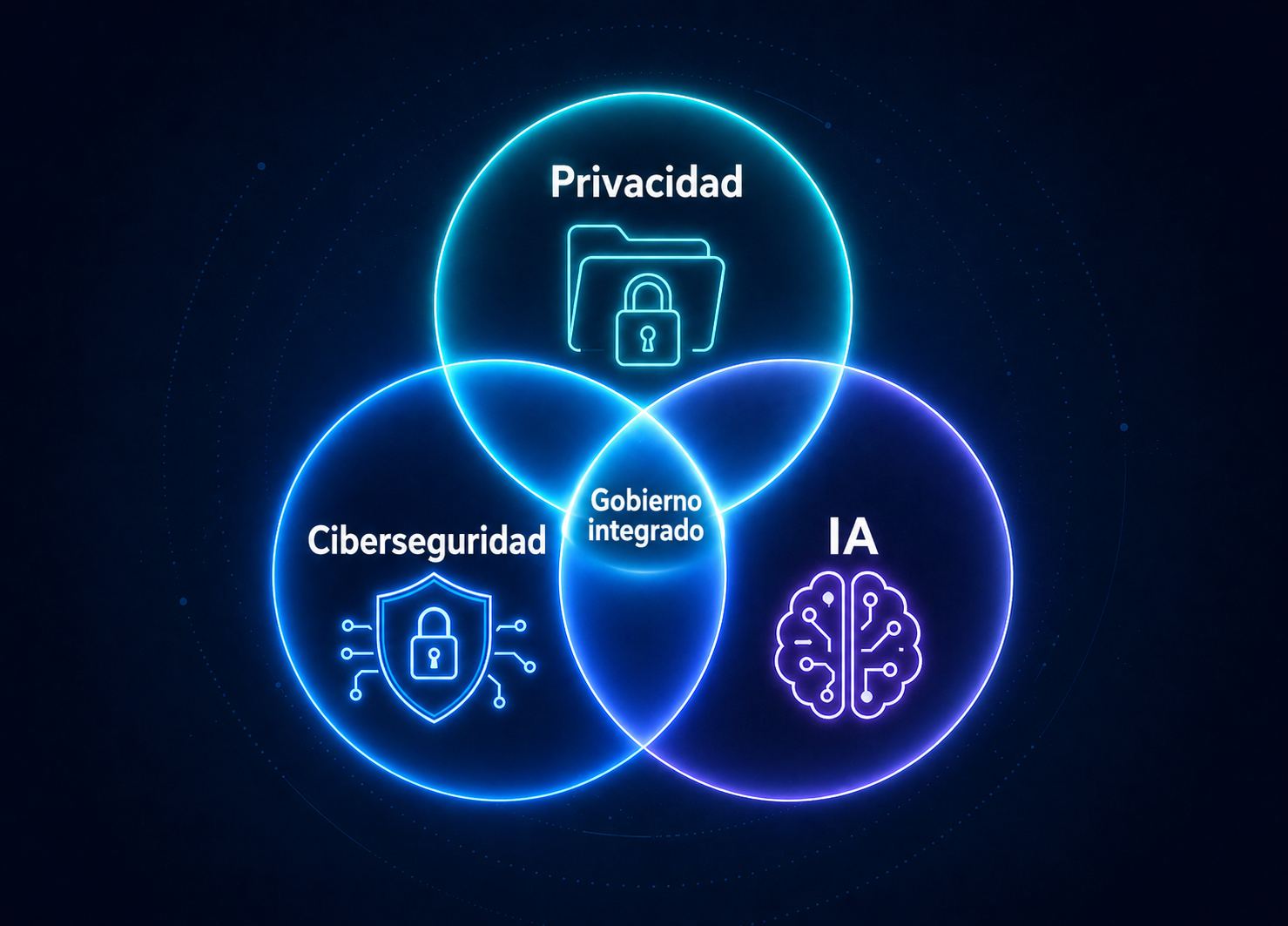
But the underlying message is one: companies need to stop managing privacy, security and artificial intelligence as separate folders.
The question for a manager or CEO is no longer “do we have GDPR documents?”. The question is whether the company can explain what data it processes, which systems protect it, what AI it uses, which providers are involved and what evidence it would preserve if tomorrow there were a claim, a breach or a dispute.
The risk map leadership should look at now
The figures are not decoration: they help decide what to organise first when privacy, security and AI compete for budget and attention.
INCIBE-CERT managed this figure in 2025, 26% more than in 2024.
Source: INCIBE, 2025 Cybersecurity BalanceThe increase confirms that pressure is not falling: incidents, fraud and the need for ordered response are rising.
Source: INCIBERelevant systems detected and notified by INCIBE due to exposure or exploitable vulnerabilities.
Source: INCIBE-CERTIt represents four out of every ten security incidents, with 19% growth compared with the previous year.
Source: INCIBEThree dates and signals already shaping decisions
- AI Act: literacy and prohibited practices AI literacy obligations and certain prohibitions are already active.
- AEPD: 32 objectives and 115 actions The annual plan includes technology privacy, a laboratory, AI and automation.
- AI Act: general application The general application of the EU AI Act makes inventory and classification urgent work.
1. Cybersecurity: the problem is no longer technical, it is operational
INCIBE's 2025 balance gives a clear picture: 122,223 cybersecurity incidents managed, 26% more than the previous year, and 237,028 relevant vulnerable systems detected and notified. Online fraud also represented four out of every ten incidents and phishing remained one of the most common forms of attack.
These figures do not describe a problem reserved for large companies. They describe a reality affecting SMEs, law firms, technology providers, regulated entities and organisations that depend on systems, email, cloud, ERP, cameras, external providers or customer portals.
Recent cases such as the cyberattack on the Port of Vigo, which forced systems to be isolated and manual processes to be used temporarily, show something important: cybersecurity is not measured only by whether an attacker gets in. It is also measured by the ability to keep operating, contain, document, recover and preserve evidence.
2. Fraud no longer arrives as a badly written email
The 2025 Spanish income tax campaign, filed in 2026, has once again become a perfect context for impersonation campaigns. In April, the Spanish Tax Agency published several phishing and smishing alerts with fake forms, domains imitating official services and messages pressuring users with alleged refunds or notices.
This matters to companies for three reasons. First, because the user remains an entry point. Second, because attacks adapt to timing and context. Third, because after the click comes the less visible part: compromised credentials, email access, invoice modification, data leakage or impersonation before customers and suppliers.
The response cannot stop at “train staff”. Training, yes, but accompanied by multi-factor authentication, access reviews, password policy, filters, backups, traceability, payment verification procedures and a clear rule for preserving evidence if something happens.
3. Europe is connecting cybersecurity and data protection
The joint EDPB and EDPS opinion on Cybersecurity Act 2 and changes to NIS2 confirms a trend: European cybersecurity is no longer understood without data protection, fundamental rights, digital identity, supply chain and risk management.
For a company, this has a practical consequence. It is not enough to deploy technical measures if they are not connected to responsibilities, providers, contracts, risk analysis, decision records and incident response. And it is not enough to have legal texts if the real systems do not support them.
ENS, ISO 27001, GDPR and NIS2 are not identical pieces, but they increasingly share the same language: assets, risks, controls, evidence, owners, continuous improvement and response capability.
4. The AI Act is landing inside companies
The EU AI Act is no longer a distant idea. The European Commission recalls that general application arrives on 2 August 2026, with exceptions already active since 2025, such as AI literacy, prohibited practices, governance and obligations for general-purpose models.
The Commission is also working on a code of practice on marking and labelling AI-generated content to facilitate compliance with transparency obligations, especially for artificially generated content, deepfakes and certain informative uses.
For leadership, the reading is simple: if a company uses AI in customer service, recruitment, scoring, video surveillance, document analysis, report generation, marketing, security or internal automation, it needs at least four things: inventory, classification, human control and documentation.
And if AI touches personal data, cameras, decisions about people or sensitive environments, privacy by design, minimisation, proportionality, security, log retention and provider review also enter the picture.
5. The AEPD is also looking at technology, AI and automation
The AEPD 2026 Action Plan includes 32 operational objectives and 115 actions. Its highlighted lines include the Privacy Laboratory, technological experimentation, the incorporation of AI tools and automation solutions in the Agency's own processes.
This does not mean every company will be inspected tomorrow. It means something more interesting: the authority is preparing capabilities for an environment where data processing is more complex, more automated and harder to explain if it has not been organised from the outset.
What a company should review now
If I had to turn all of the above into an executive list, I would start here:
- Real inventory of data, systems and AI.What is processed, where it is, who accesses it, which provider is involved and which automated decisions exist.
- Breach and incident procedure.Who decides, how containment works, what is documented, when notification is needed and how evidence is preserved.
- Critical access review.Email accounts, administration, ERP, cloud, VPN, backups, cameras and tools with sensitive data.
- Contracts and processors.Technology providers, hosting, software, AI, maintenance, video surveillance and external support.
- Continuity and recovery.Tested backups, alternative systems, useful logs and minimum operating capability if something fails.
- AI governance.Classification, purpose, data used, human oversight, transparency and security measures.
A company that organises privacy, cybersecurity and AI before conflict gains something more valuable than “compliance”: it gains decision-making capability.
That is the point. It is not about frightening people with sanctions or filling a folder. It is about enabling leadership to look at a digital risk and answer clearly: what is happening, what impact it has, what evidence exists, which obligation is triggered and what decision must be made.
Frequently asked questions
¿Qué tienen en común INCIBE, AEPD y AI Act en 2026?
Apuntan a la misma conclusión para dirección: privacidad, ciberseguridad e inteligencia artificial ya no pueden gestionarse como áreas aisladas. INCIBE gestionó 122.223 incidentes en 2025 (+26% interanual), la AEPD ha publicado un Plan de Actuación 2026 con 32 objetivos y 115 acciones muy orientadas a tecnología, IA y automatización, y la aplicación general del AI Act llega el 2 de agosto de 2026.
¿Cuándo es exigible el AI Act de forma general?
La aplicación general del Reglamento Europeo de IA llega el 2 de agosto de 2026. Algunas obligaciones —alfabetización en IA, prácticas prohibidas, gobernanza y obligaciones para modelos de propósito general— ya están activas desde el 2 de febrero de 2025.
¿Qué debería revisar dirección antes de un incidente?
Seis frentes: inventario real de datos, sistemas e IA; procedimiento de brechas e incidentes; revisión de accesos críticos; contratos y encargados; continuidad y recuperación; y gobierno de IA (clasificación, supervisión humana, transparencia y seguridad). Lo importante no es solo cumplir, sino poder explicar qué se decidió, cuándo y con qué base.
¿Por qué el fraude online preocupa más en 2026?
Porque ya no llega como un correo mal escrito. Las campañas se adaptan al contexto —por ejemplo, suplantaciones aprovechando la campaña de la Renta— y, tras el clic inicial, lo que viene son credenciales comprometidas, modificación de facturas, fuga de datos y suplantación ante clientes y proveedores. Según INCIBE, el fraude online representó cuatro de cada diez incidentes en 2025.
¿Qué empresas deben prestar atención a NIS2 y al Cybersecurity Act 2?
La línea europea conecta cada vez más ciberseguridad y protección de datos: el dictamen conjunto del EDPB y el EDPS sobre Cybersecurity Act 2 y NIS2 confirma que ya no se entiende una sin la otra. Para las empresas afectadas, no basta con desplegar medidas técnicas si no están conectadas con responsabilidades, proveedores, contratos, análisis de riesgo, registro de decisiones y respuesta a incidentes.
Sources consulted
- INCIBE: 2025 cybersecurity balance
- Spanish Tax Agency: phishing detected on 22 April 2026
- Spanish Tax Agency: impersonation cases detected in 2026
- EDPB and EDPS: Joint Opinion 4/2026 on Cybersecurity Act 2 and NIS2
- European Commission: AI Act regulatory framework
- European Commission: code of practice on AI-generated content
- AEPD: 2026 Action Plan
- Cadena SER: cyberattack on the Port of Vigo
Privacy, security and AI can be organised before they become urgent.
If your company needs to review GDPR, cybersecurity, ENS/ISO 27001, the AI Act or digital evidence, I can help you bring it down to earth with legal, technical and expert evidence judgement.